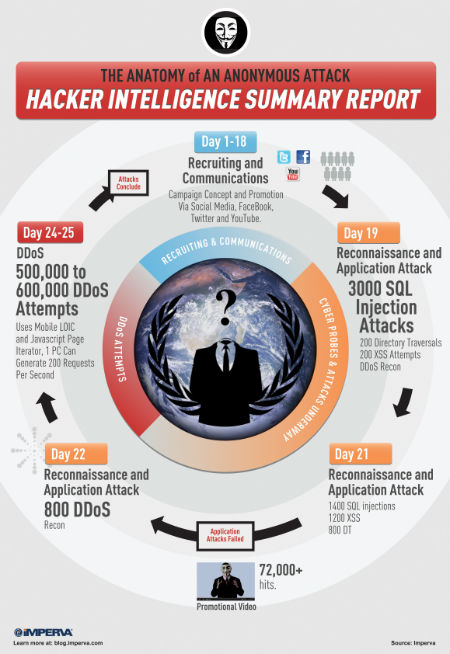
Last year, hacker group ‘Anonymous’ attacked Security firm Imperva’s application defense center for 25 days. Yesterday Imperva released a report detailing the anatomy of an Anonymous attack, using data gleaned from their first hand experience. By analyzing traffic logs from the days of their attack, Imperva believes they were able to identify patterns and trends that can help companies understand and prepare for a future attack, if they should become an Anonymous target.
In their report, Impreva describes the two categories of attacks ( Imperva’s attack was the latter):
› Reactive: In this case, some incident inspired the members of Anonymous to attack a target. For example, when MasterCard, Visa and others stopped allowing payments to Wikileaks, Anonymous began Operation Payback intended to bring down websites with excessive traffic. When BART police blocked the use of cell phones in certain stations, Anonymous hacked into BART computers, exposing the data of dozens of employees.
› Proactive: In this case, Anonymous announces an intention to attack a target. Significantly less common, there have only been a few incidents. For example, threats against Facebook and Mexican drug lords were made, but attacks either fizzled or never even materialized. It is difficult to estimate
The report also separates the hacker group into two categories as well:
> Skilled hackers — In this campaign, we witnessed a small group of skilled hackers. In total, this group numbered no more than 10 to 15 individuals. Given their display of hacking skills, one can surmise that they have genuine hacking experience and are quite savvy.
>Laypeople — This group can be quite large, ranging from a few dozen to a few hundred volunteers. Directed by the skilled hackers, their role is primarily to conduct DDoS attacks by either downloading and using special software or visiting websites designed to flood victims with excessive traffic. The technical skills required range from very low to modest.
In Imperva’s attack, they identified a 10:1 ratio of laypeople to skilled hackers.
Other interesting claims were made about Anonymous’ hacker toolbox: The security firm believes the hackerism group has built a custom-attack software which can use from computers as well as mobile devices, but also claims that the group also uses “inexpensive, off-the-shelf tools as opposed to inventing new techniques or developing complex attacks.” The report notes that the attacks use the attack did not entail malware or phishing/spear phishing , and while bots are sporadically used they were not used in Imperva’s attack.
The bulk of the report was spent detailing the lifecycle of an Anonymous attack which Imperva has put together in the infographic below.